SEC504: Hacker Tools, Techniques, and Incident Handling


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usConnect, learn, and share with other cybersecurity professionals
Engage, challenge, and network with fellow CISOs in this exclusive community of security leaders
Become a member for instant access to our free resources.
Sign UpMission-focused cybersecurity training for government, defense, and education
Explore industry-specific programming and customized training solutions
Sponsor a SANS event or research paper
We're here to help.
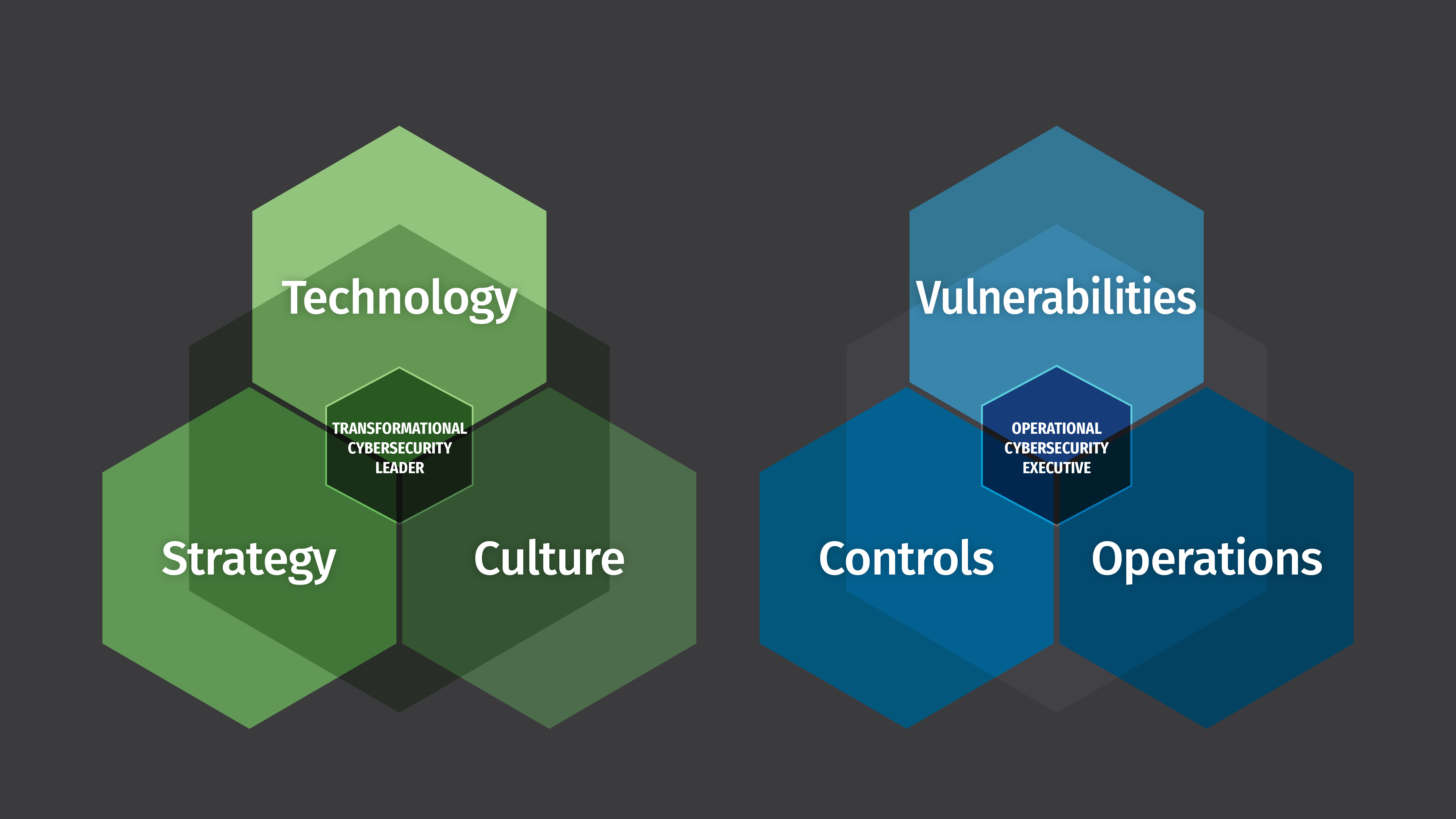
Contact UsGo Beyond Good Enough. Become A Transformational Leader or an Operational Cybersecurity Executive.
In an effort to help our students find the right career path and/or training for their current responsibilities, SANS Cybersecurity Leadership Curriculum has created two course and certification triads that align to help create stronger, more well-rounded cybersecurity leaders.
Each triad is explained in more detail below, as well as information about the webcast / blog series digging into each triad in great detail.
With corporations in need of protecting against an endless and increasing onslaught of information security threats, technology management skills alone are no longer sufficient. Today it is about technology, business strategy, and people. Cybersecurity leaders need to be up to speed on information security issues from a technical standpoint, understand how to implement security planning into the broader business objectives, and be able to build a longer lasting security and risk-based culture. Adjusting employees’ and leadership’s way of thinking about security in order to prioritize and act to prevent today’s most common cybersecurity attacks requires organizational change that affects the foundational culture of the organization.
A Transformational Cybersecurity Leader will be able to:
The Transformational Cybersecurity Leader triad ensures a cyber security manager is proficient in all three key pillars by providing a complete, curated package of education to support you along your path to becoming the strongest cybersecurity leader possible in today’s dynamic, online world.
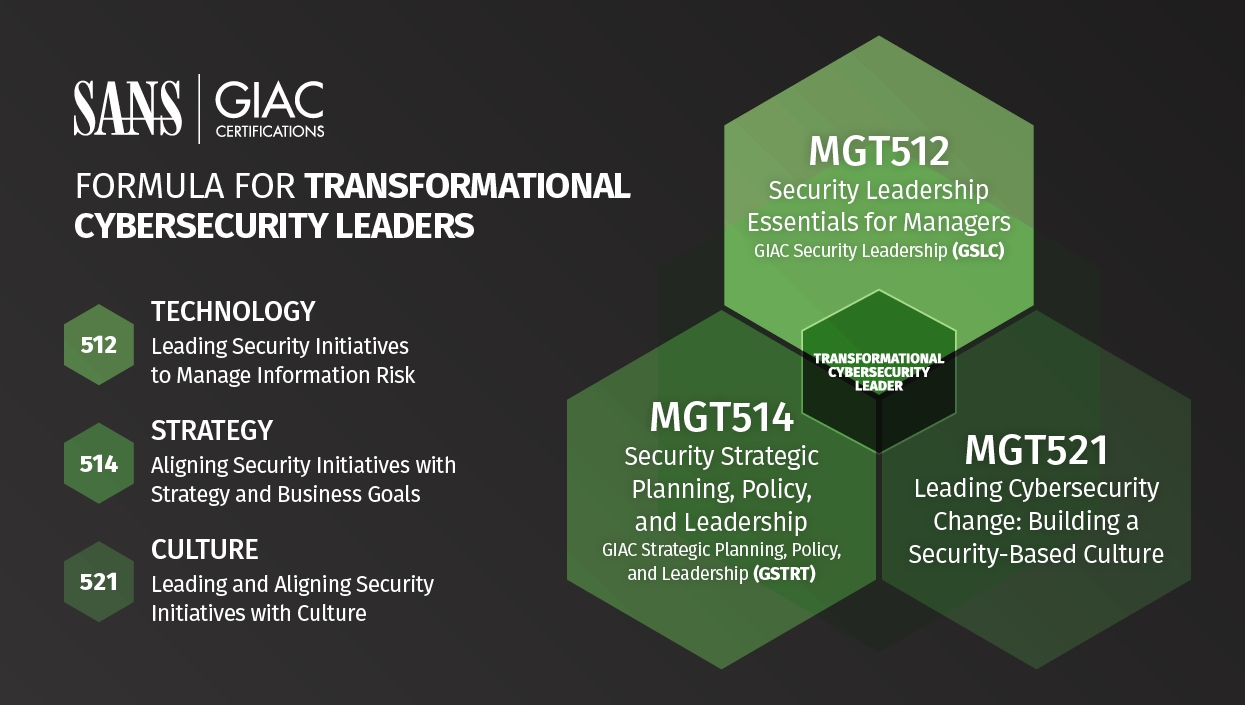
Security Manager | Director | Information Security Officer
This course empowers student to become effective security managers and quickly grasp critical information security issues and terminology, with a focus on security frameworks, computer/network security, vulnerability management, cryptography, data protection, security awareness, application security, DevSecOps, cloud security, security operations.
Security Manager | Director | Information Security Officer | CISO
This course gives you tools to become a security business leader who can build and execute strategic plans that resonate with other business executives, create effective information security policy, and develop management and leadership skills to better lead, inspire, and motivate your teams.
Security Awareness Manager | Information Security Officer | CISO | Risk Officer
Drawing on real-world lessons from around the world, this course will teach you how to leverage the principles of organizational change in order to develop, maintain, and measure a security-driven culture. Through hands-on instruction and a series of interactive labs and exercises, you will apply the concepts of organizational change to a variety of different security initiatives and quickly learn how to embed security into your organization's culture.
As cyber attacks become more common and more expensive, many organizations are making a foundational shift to view operations from the point of view of an adversary, in order to protect their most sensitive information. Despite vulnerability tools and programs being available for several decades, breaches still happen regularly from known vulnerabilities. With a wide range of technologies in use requiring more time and knowledge to manage, a global shortage of cybersecurity talent, an unprecedented migration to cloud, and legal and regulatory compliance often increasing and complicating the matter more, it’s no wonder we've seen frustration in the eyes of information assurance engineers, auditors, SOC analysts, and cybersecurity managers who are trying to make a difference in their organizations by better defending their data systems. Some organizations even wonder if they will ever succeed at properly protecting their information. Do not give up! The SANS Operational Cybersecurity Executive triad is here to help you build, grow, and sharpen your cyber defense team!
An Operational Cybersecurity Leader will be able to:
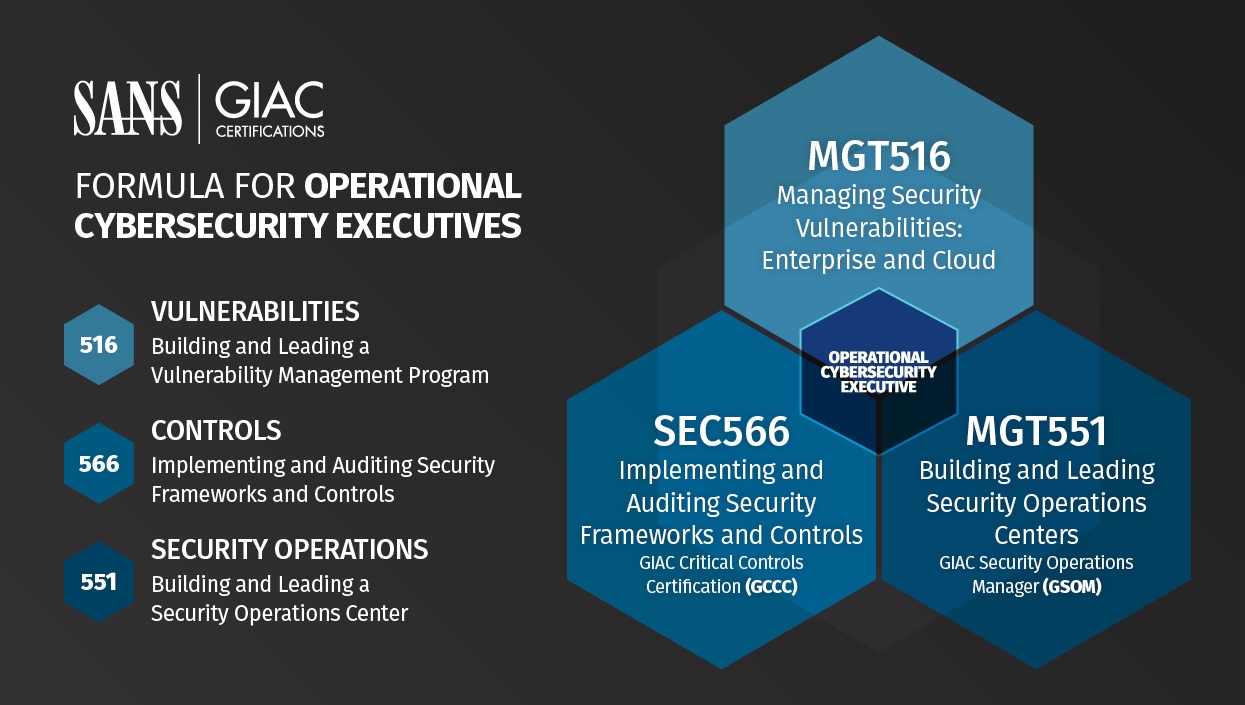
Security Manager | Architect | Director | Information Security Officer
This course will help you think more strategically about vulnerability management so you can mature your organization's program. By understanding common issues and their solutions, you will be better prepared to meet the challenges of today and tomorrow. Through class discussions and other hands-on exercises, you will learn specific analysis and reporting techniques that will enable you to effectively communicate the problems you and your peers are facing and how they can be solved.
Security Manager | Information Assurance Auditors | Security Officer
As threats evolve, an organization's security should, too. To enable your organization to stay on top of this ever-changing threat scenario, SANS has designed a comprehensive course on how to implement the Critical Security Controls, a prioritized, risk-based approach to security. Designed by private and public sector experts from around the world, the Controls are the best way to block known attacks and mitigate damage from successful attacks. They have been adopted by the U.S. Department of Homeland Security, state governments, universities, and numerous private firms.
SOC Manager | SOC Lead | SOC Engineer | Architect
With lessons from those who have been in the trenches for years, this course will help you define, implement and sharpen your organization's cyber defense. Students work on hands-on exercises covering everything from playbook implementation to use case database creation, attack and detection capability prioritization and visualization, and purple team planning, execution, and reporting. Attendees will leave with a framework for understanding where their SOC should be focusing its efforts, how to track and organize defensive capabilities, and how to drive, verify, and communicate SOC improvements.
The webcast series outlined below are based on the fictitious Rekt Casino. It fell victim to a ransomware attack which resulted in personal identifiable information, HR records, and financial information being exfiltrated. The root cause of the problem was a lack of governance, risk, and compliance, along with properly configured technical and administrative controls. It could also be argued that Rekt Casino lacked a strategic plan as well as an inherent security culture. Looking at the history of Rekt Casino we are going to identify when the transition from the old school approach of information security could have been transitioned to the enterprise risk management approach.
The mistake organizations often make is to focus on defenses such as endpoint protection, firewalls, and intrusion prevention without a good understanding of what the threats actually are. It’s as if Rekt Casino fortified their castle to protect against bows and arrows, yet the adversaries attacked with a trebuchet.
If the executives, technology team, and board of directors had been paying attention to news stories, security guidance, employees’ approach to protecting company assets, or even attending security related conferences, they would have gotten the message that security had become a critical concern due to the threat landscape. It’s not enough to acknowledge that security requires more attention, you also have to act on that knowledge.
WEBCAST SERIES: Rekt Casino Hack Assessment Transformational Cybersecurity Leader
BLOG SERIES: Rekt Casino Hack Assessment Transformational Cybersecurity Leader
WEBCAST SERIES: Rekt Casino Hack Assessment Operational Cybersecurity Executive
BLOG SERIES: Rekt Casino Hack Assessment Operational Cybersecurity Executive