SEC504: Hacker Tools, Techniques, and Incident Handling


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usConnect, learn, and share with other cybersecurity professionals
Engage, challenge, and network with fellow CISOs in this exclusive community of security leaders
Become a member for instant access to our free resources.
Sign UpMission-focused cybersecurity training for government, defense, and education
Explore industry-specific programming and customized training solutions
Sponsor a SANS event or research paper
We're here to help.
Contact UsIt usually takes an incident such as ransomware to change an organization’s focus and approach on how they view security, but where do they start?

This is Part II of a 3-part blog series based on MGT514: Security Strategy, Policy, and Leadership.
Read Part I here. Read Part II here.
Now that we have industry standard frameworks to follow, we can focus on getting Rekt Casino secure and operational.
At this point, we have enough information that can be used to establish a strategic plan for security. We’ll now develop the road map to becoming more secure.
We’ll take the data from our postmortem, SWOT Analysis, and PESTAnalysis and create a Gap Analysis.
The Gap Analysis is comprised of determining the current state, the desired future state, and changes or initiatives needed to get to the future state.
A Gap Analysis for Rekt Casino would look similar to this:
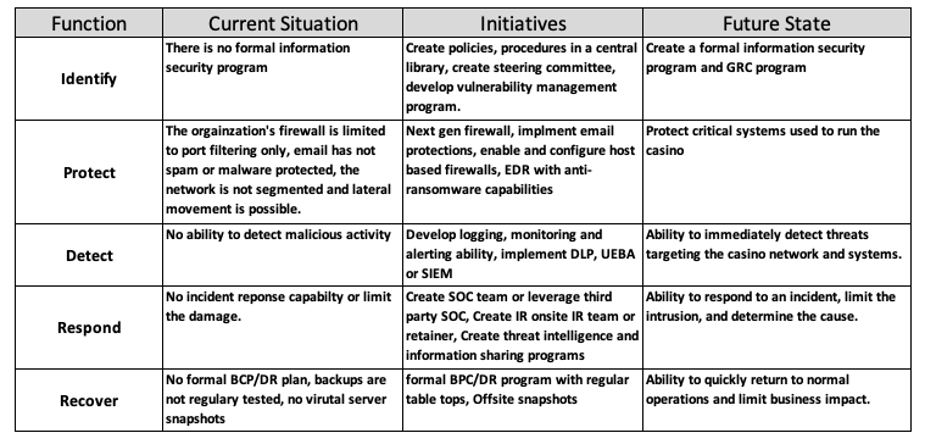
Figure 9: Gap Analysis
The Gap Analysis approach is to first define the current state, then define the future state of where you would like to go. You then come back to the center of that chart and decide what those initiatives should be.
As you can see from the above Gap Analysis, Rekt has a lot of changes to make to become secure. Also notice that in the left-hand column, we focused specifically on the activities in the NIST CSF.
We now know what needs to be done to become more secure, but where do we start?
That’s where we’ll use a Decision Matrix Analysis to inform how to best approach these new Initiatives.
A Decision Matrix Analysis allows you to rank multiple factors to inform the best decision. For Rekt Casino we will be using the following key factors:
We will rank each of these factors from 0-5. The lower the number, the least desirable that factor is.
The resulting Decision Matrix Analysis could look similar to this:
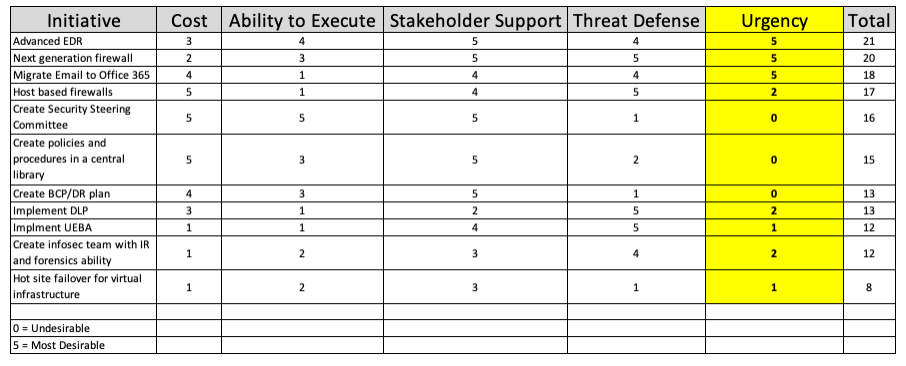
Figure 10: Decision Matrix Analysis
I’ll explain some examples the above Decision Matrix Analysis.
Starting with Advanced EDR:
Let’s skip down to Host based firewalls:
You’ll notice I’ve added a 5th column called Urgency. This isn’t a column that would normally be present, but in a post-breach scenario there may be a need for immediate technical controls to secure the environment before recovery can begin.
In this scenario the urgent need for Advanced EDR is a 5, because getting it soon is most desirable. The urgent need for host-based firewalls is a 2, because there’s not an immediate need for that during the recovery process. Host-based firewalls can be implemented later down the road.
To determine which initiatives to start with, we’ll sort the totals from highest to lowest in the far-right side column.
The Decision Matrix Analysis dictates we should proceed in the following order:
If you look at the implementation order, you might be wondering why creating a steering committee, policies and procedures come before DLP (Data Loss Prevention) and UEBA (User and Entity Behavior Analytics).
The reason for that is, part of the policy and procedure process will be data classification and data access permissions. You need to define those to implement DLP correctly.
You also need that before UEBA because part of what UEBA does in the first stage of deployment is establish a baseline of what normal activity looks like. If you don’t have the appropriate baseline permissions, you can’t effectively determine what normal behavior looks like.
Now that the initiatives and order of implementation have been established, you need to think about stakeholder management. All of these initiatives are going to affect a wide range of stakeholders.
It’s important to manage the expectations of stakeholders because they hold key information for your initiatives. Stakeholders can influence the organizational perspective, support you, or block you. Many strategic initiatives have failed due to poor stakeholder management.
We’ll approach stake holder management using two tools, a SIPOC Matrix, and a Power/Interest Grid. SIPOC stands for Suppliers, Inputs, Processes, Outputs, and Customers.
Figure 11: Blank SIPOC Matrix
We will use the SIPOC Matrix above to determine who the stakeholders are for the AdvancedEDR initiative:
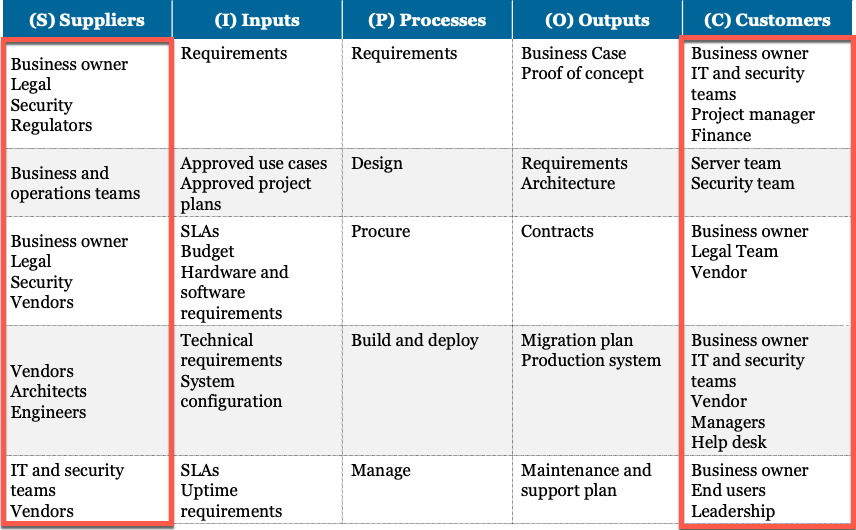
Figure 12: Completed SIPOC Matrix
We’ll now map the stakeholders by title in a Power/Interest Grid:
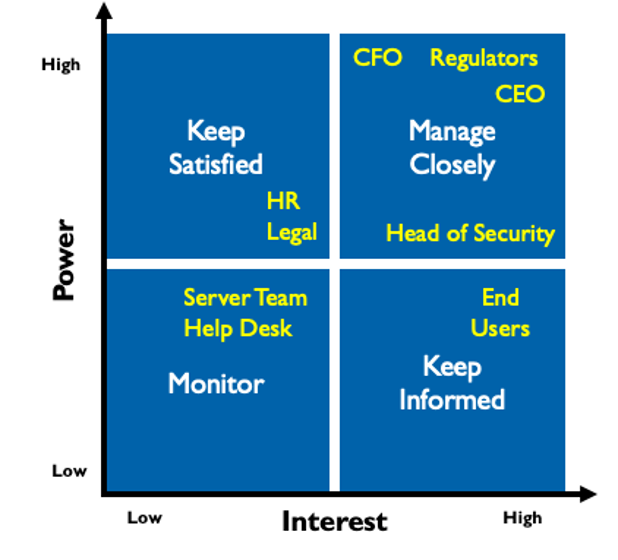
Figure 13: Power/Interest Grid
The left-hand side is the amount of power the stakeholder has. The bottom is amount of interest the stakeholder has.
This is a high-level approach to building an information security program in a post-breach scenario. This approach includes the basic steps for building a mature information security program.
SANS MGT514: Security Strategic Planning, Policy, and Leadership goes more in depth how to align your information security program with the goals of the organization and bridge the gap between the technical and business objectives.
This is not a one-size-fits all approach. Depending on the industry you are in the approach needs to be tailored and have the appropriate context applied.
This post is based on a post-breach scenario of an organization that had little in place to start with. If you aren’t in a similar scenario, this approach can be used to improve your existing information security program.
This is Part II of a 3-part blog series based on MGT514: Security Strategy, Policy, and Leadership.
Read Part I here. Read Part II here.
Joe Sullivan has over 20 years of experience in information security. Joe is Principal Consultant at Rural Sourcing in Oklahoma City where he manages and develops the security consulting services and the teams that provide them. Over his career Joe has worked in incident response, penetration testing, systems administration, network architecture, forensics, and is a private investigator specializing in computer crime investigations. Joe teaches MGT514: Security Strategic Planning, Policy, and Leadership.


Joe Sullivan has over 20 years of experience in information security and is a senior security consultant for TrustedSec. Joe teaches LDR514: Security Strategic Planning, Policy, and Leadership.
Read more about Joe Sullivan